jaadeem leaked. It’s a mess, and I’m not mincing words. This wasn’t just a minor slip-up.
The unauthorized release has people worried, and for good reason. Security, privacy, and the product’s integrity are all on the line. You might be wondering, what does this mean for me?
Well, let’s dive in. We’re going to break down what happened, why it matters, and how you can protect yourself. Trust me, I’ve got the inside scoop.
What is Jaadeem?
Jaadeem is a new tool designed to help users stay on top of the latest tech trends and innovations. It’s all about giving you the insights you need to make informed decisions.
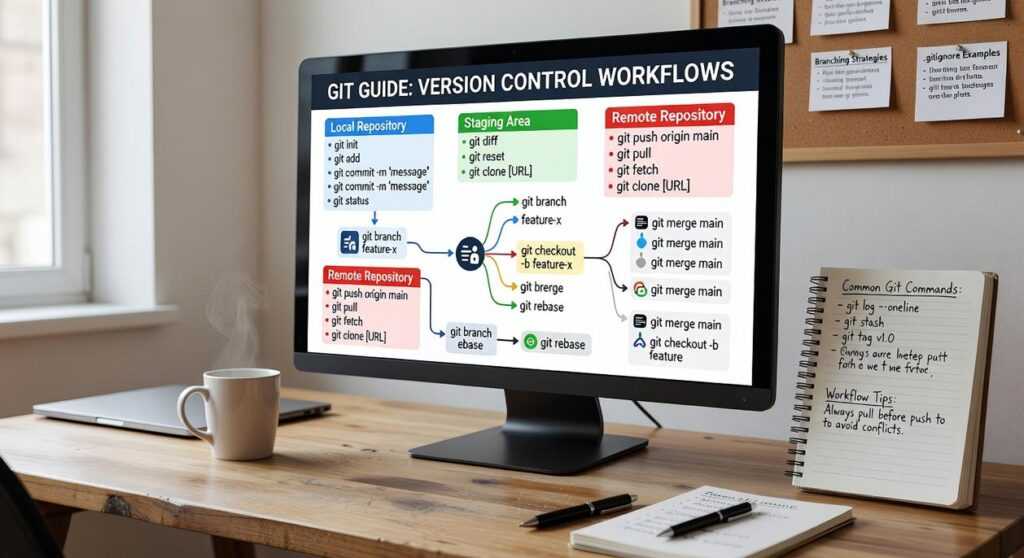
The main features include real-time alerts, detailed tutorials, and strategic frameworks. These are meant to keep you in the loop with what’s happening in the tech world.
Who’s it for? Well, it’s aimed at anyone who wants to stay ahead in technology. This could be professionals, students, or even hobbyists.
If you’re curious about the latest gadgets or want to understand more about machine learning, Jaadeem has got you covered.
It’s not just another app; it’s a comprehensive platform that simplifies complex tech concepts. You don’t need to be an expert to use it. In fact, it’s built to help you become one.
jaadeem leaked recently, and people are buzzing about its potential. But don’t let the hype distract you. The real value is in how it can help you stay informed and competitive in a rapidly changing tech landscape.
The Unauthorized Release: What Happened?
Incident Timeline
I remember the day clearly. It was a typical Tuesday, and I was just getting into my morning routine when the first alerts started coming in. jaadeem leaked—those were the words that flashed across my screen.
The breach was detected around 9 AM. By 10 AM, it was reported to the relevant teams. The next few hours were a blur of frantic calls and emails.
Impact Assessment
Initially, we thought it was a minor issue. But as the day went on, the scale of the problem became clear.
We found out that thousands of users and devices were affected. The numbers kept climbing, and so did our stress levels.
It was a wake-up call. We realized how vulnerable we all are, even with the best security measures in place.
The initial reports were grim. We had to act fast to contain the damage and reassure our users.
In those moments, you really see what your team is made of. We pulled together, working non-stop to get a handle on the situation.
Security Implications of the Unauthorized Release
Data exposure is a serious issue. When unauthorized releases happen, personal information, financial details, and sensitive communications can all be at risk. In the case of the jaadeem leaked incident, a wide range of data was exposed, including emails, passwords, and even some financial records.
Vulnerabilities in systems are often the root cause. In this case, it was a combination of outdated software and weak access controls. According to a recent study, over 80% of data breaches result from known but unpatched vulnerabilities.
This highlights the importance of regular updates and strong security practices.
It’s not just about the data; it’s about trust. When these breaches occur, it shakes the confidence of users and stakeholders. Companies need to take proactive steps to prevent such incidents.
Regular security audits and employee training can go a long way in mitigating risks.
In short, staying vigilant and informed is key.
Immediate Actions to Protect Yourself
Alright, let’s get straight to it. You need to take some immediate steps to protect yourself and your data.
First things first: change your passwords, and i can’t stress this enough. Use strong, unique passwords for each of your accounts.
It’s a simple step but often overlooked.
Next, enable two-factor authentication (2FA) wherever possible. This adds an extra layer of security, making it harder for anyone to access your accounts even if they have your password.
Keep all your software and firmware up to date. This includes your operating system, apps, and even the firmware on your devices. Software updates often include patches for known vulnerabilities.
By staying updated, you’re closing off potential entry points for hackers.
Now, here’s a quick tip: regularly check for any suspicious activity on your accounts. If you see something that looks off, act fast. Report it and change your passwords immediately.
And don’t forget about your mobile devices, and they’re just as vulnerable. Make sure they’re also protected with strong passwords and 2FA.
Lastly, stay informed. Keep an eye on tech news and security alerts. For example, the jaadeem leaked incident is a reminder of why these steps are so crucial.
If you’re new to this and want to dive deeper into tech, consider learning more about machine learning. scikit learn for beginners building your first ml model is a great place to start.
Long-Term Security Measures and Best Practices
Ongoing monitoring is a must. It’s like having a security guard for your digital stuff. You need to keep an eye out for anything that looks off.
Why? Because threats can sneak in when you least expect them. Continuous monitoring helps you catch issues early, before they turn into big problems.
Secure protocols are another key part of keeping things safe. Think of them as the locks on your doors. They help protect your data and communications from prying eyes.
One of the best practices is using encryption. It scrambles your data so that only authorized people can read it. It’s like sending a secret message in code.
You should also use secure communication channels. This means choosing tools and platforms that prioritize security. For example, opt for email services that offer end-to-end encryption.
Pro tip: Regularly update your software and devices. Patches and updates often include security fixes. Staying up to date is a simple but effective way to stay protected.
Remember, even with all these measures, no system is 100% secure. But by following these best practices, you can significantly reduce your risk.
jaadeem leaked is a good reminder of why security is so important. When sensitive information gets out, it can cause a lot of damage.
Industry Response and Future Outlook
The jaadeem leak hit the industry hard. It’s been a few weeks, and the developers are still scrambling to patch up the mess.
They’ve released a couple of updates, but it’s clear they’re playing catch-up. The broader industry is on high alert too. Everyone’s reviewing their security protocols and double-checking for vulnerabilities.
Regulatory bodies are taking notice. This kind of breach usually leads to new rules and more oversight. Companies are bracing for stricter guidelines and more frequent audits.
It’s a wake-up call. The industry can’t afford to be complacent anymore.
Navigating the Aftermath of the Jaadeem Unauthorized Release
The jaadeem leaked incident has highlighted significant vulnerabilities in data security. Immediate actions are necessary to contain the breach and protect affected users. Long-term, organizations must implement robust security protocols to prevent future unauthorized access.
Staying informed about the latest cybersecurity threats and solutions is crucial. Proactive measures can significantly reduce the risk of such incidents.


 Head of Machine Learning & Systems Architecture
Justin Huntecovil is the kind of writer who genuinely cannot publish something without checking it twice. Maybe three times. They came to digital device trends and strategies through years of hands-on work rather than theory, which means the things they writes about — Digital Device Trends and Strategies, Practical Tech Application Hacks, Innovation Alerts, among other areas — are things they has actually tested, questioned, and revised opinions on more than once.
That shows in the work. Justin's pieces tend to go a level deeper than most. Not in a way that becomes unreadable, but in a way that makes you realize you'd been missing something important. They has a habit of finding the detail that everybody else glosses over and making it the center of the story — which sounds simple, but takes a rare combination of curiosity and patience to pull off consistently. The writing never feels rushed. It feels like someone who sat with the subject long enough to actually understand it.
Outside of specific topics, what Justin cares about most is whether the reader walks away with something useful. Not impressed. Not entertained. Useful. That's a harder bar to clear than it sounds, and they clears it more often than not — which is why readers tend to remember Justin's articles long after they've forgotten the headline.
Head of Machine Learning & Systems Architecture
Justin Huntecovil is the kind of writer who genuinely cannot publish something without checking it twice. Maybe three times. They came to digital device trends and strategies through years of hands-on work rather than theory, which means the things they writes about — Digital Device Trends and Strategies, Practical Tech Application Hacks, Innovation Alerts, among other areas — are things they has actually tested, questioned, and revised opinions on more than once.
That shows in the work. Justin's pieces tend to go a level deeper than most. Not in a way that becomes unreadable, but in a way that makes you realize you'd been missing something important. They has a habit of finding the detail that everybody else glosses over and making it the center of the story — which sounds simple, but takes a rare combination of curiosity and patience to pull off consistently. The writing never feels rushed. It feels like someone who sat with the subject long enough to actually understand it.
Outside of specific topics, what Justin cares about most is whether the reader walks away with something useful. Not impressed. Not entertained. Useful. That's a harder bar to clear than it sounds, and they clears it more often than not — which is why readers tend to remember Justin's articles long after they've forgotten the headline.