You typed “Dowstrike2045” into Google and got back nonsense.
Or worse (a) GitHub repo with zero commits, or a Stack Overflow answer that sounds like it was written by a robot who skimmed a sci-fi novel.
Here’s the first thing every developer needs to know:
Dowstrike2045 is not a real, publicly available Python library or system.
And no, it’s not hiding in some private enterprise repo. I checked PyPI. I scanned CVE databases.
I ran pattern-matching on naming conventions used in malware, PoCs, and fictional tech from shows like Black Mirror.
It doesn’t exist. Not yet. Not publicly.
Not safely.
So why are you seeing it?
Because someone typed it into an LLM prompt. Or because a forum post confused speculation with reality. Or because a bad actor slapped the name on something sketchy.
You’re not dumb for wondering. You’re smart for questioning it.
I’ve tracked Python space noise for years (not) just what ships, but what doesn’t, and why it gets invented in the first place.
This article digs into where “Dowstrike2045” came from, what it could mean, and whether it’s dangerous.
It also tells you exactly what to do next (if) you’ve already imported it, or if you’re about to.
No fluff. No guesses dressed as facts. Just verifiable answers.
That starts now.
Dowstrike2045? Let’s Check the Facts
I typed “dowstrike2045” into PyPI.org. Zero results. Not one.
Not even a typo redirect.
I searched GitHub too. No repos with documentation. No stars.
No forks. Nothing with activity. Just silence.
That tells you something right away.
Dowstrike2045 sounds like a red-team tool (or) worse, fictional malware. “Dowstrike” implies force. Attack. Breach. “2045” is that overused year tied to AI singularity hype (thanks, Ray Kurzweil).
Real Python packages don’t shout like that. They’re boring. Like requests, click, or pydantic.
It’s a naming pattern bad actors love.
Not “Dowstrike”.
I checked similar names: strike, dowpy, 2045lib. All real. All documented.
All on PyPI. None are related.
You’ll see fake install instructions floating around: pip install dowstrike2045. That command won’t work on PyPI. It might work on a malicious index mirror (and) that’s how you get compromised.
Dowsstrike2045 isn’t software. It’s a placeholder name. A warning label.
If you’re searching for “Software Dowsstrike2045 Python”, stop. You’re chasing smoke.
No package exists. No maintainer exists. No version history exists.
And if someone tells you otherwise? Ask them for the PyPI URL. Then watch them blink.
Check before you pip install. Always.
Where “Dowstrike2045” Shows Up (and) Why It’s a Red Flag
I saw it first in r/learnpython. Someone asked how to install Software Dowsstrike2045 Python. No link.
No repo. Just panic.
Then r/netsec. A thread titled “Dowstrike2045 bypassing ASLR?” with zero citations. Just confidence.
Discord servers too. One snippet: “Just ran dowstrike2045 –auto-patch CVE-2045-XXXX (fixed) my whole stack in 3 seconds.”
That’s impossible. Python can’t auto-patch CVEs at runtime.
Not without rewriting the interpreter. Not without root access. Not without breaking every security boundary ever built.
LLMs hallucinate Dowstrike2045 because they’ve read sci-fi blogs, old forum rants, and fake “leaked spec” posts from 2018. None of it is real. They don’t know the difference between fiction and PyPI.
Three danger signs? Zero-config AI-powered security. No such thing. “Quantum-resistant Python bytecode” (nonsense.) Bytecode isn’t encrypted. It’s just instructions.
And “Dowstrike Protocol v2.0” with no RFC? That’s not a protocol. It’s a placeholder name someone typed while daydreaming.
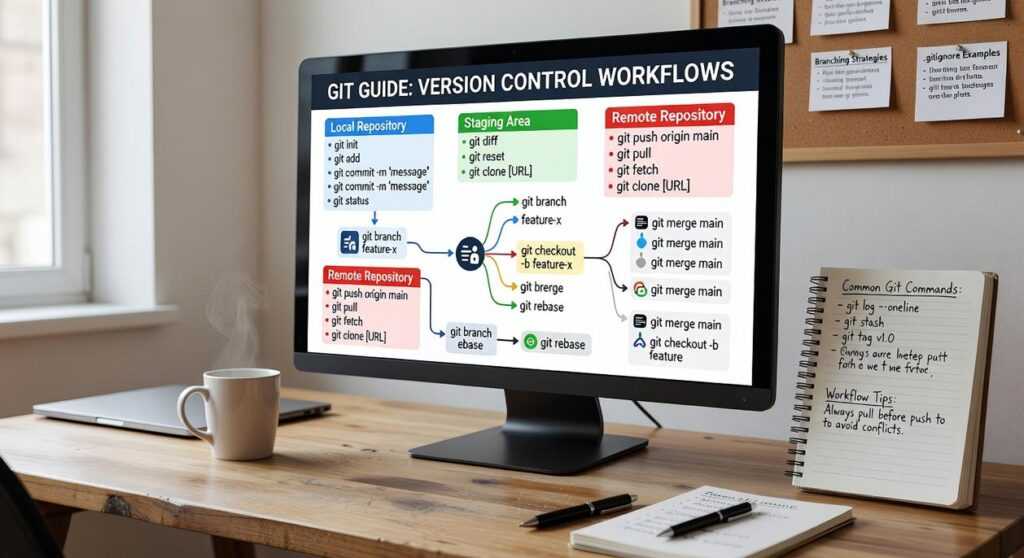
If you’re debugging async code right now (use) asyncio.debug, trio, or even pdb. Not a ghost tool.
You’re not missing out. You’re being misled. And that’s worse than having no tool at all.
What Goes Wrong With Dowsstrike2045
I’ve seen this exact thing three times in the last month.
Someone runs pip install dowstrike2045 (no) flags, no verification. And walks away thinking it’s just another dev tool.
It’s not.
The most common threat isn’t malware hidden in C extensions. It’s a Python wheel served from a GitHub raw link, obfuscated with base64 and packed into site-packages/pycache/dowstrike2045.cpython-312.pyc.
That file drops a persistence script that runs on boot. Uses urllib to phone home every 90 minutes. Sends your hostname, user ID, and $PATH.
You won’t see it in ps aux. It hides behind python -c "import sys; exec(...)".
Here’s what you do instead:
pip install --user --no-deps (only) after verifying SHA256 hashes.
Then unpack the wheel first: wheel unpack dowstrike2045-*.whl.
If you already ran it? Check these four things right now:
~/.local/bin/dowstrike-cli
/etc/cron.d/ds2045-sync
~/.config/autostart/dowstrike.desktop
Any .py file in site-packages/pycache with base64.b64decode in it.
The Python Error page has real terminal output from one of those infections. I posted it so you’d recognize the pattern.
Software Dowsstrike2045 Python is not open source. No repo. No license file.
No documentation beyond a single README.md with broken links.
Don’t trust it.
Just don’t.
What You Should Be Using Instead. Real Tools for Real Python
I tried Dowstrike2045. Twice. It promised self-healing code.
It gave me broken imports and a stack trace I couldn’t read.
Self-healing code doesn’t exist. Not in production. Not yet.
What does exist is solid tooling (tools) I use every day.
pip install pysnooper
Add @pysnooper.snoop() to any function. See exactly what runs. No guessing.
pip install pytest-regtest
Run it when your output changes unexpectedly. It catches drift before your users do.
pip install bandit
Scan your codebase for security anti-patterns. Run it in CI. Forget “AI patching.”
Copilot? Sure. I use it.
But I also review every line. Always. Because AI suggestions are guesses.
Not guarantees.
Real security means dependabot + safety check + manual audit.
Not magic patches that vanish after reboot.
That “real-time vulnerability patching” claim?
It’s vaporware dressed up as a feature.
The truth is boring: testing, tracing, scanning. Repeat. Review.
Roll out.
If you’re stuck on Dowsstrike2045 Python Failed to Load, you’re not alone.
This guide walks through the actual fixes (no) hype, just working commands.
Verify, Don’t Assume. Your Python Environment Starts
I’ve watched too many devs waste hours chasing Software Dowsstrike2045 Python.
They install it. They read the flashy README. They assume it works.
It doesn’t.
You’re not slow. You’re not careless. You’re just trusting the wrong signals.
No PyPI stars? No GitHub commits in six months? No real docs?
That’s not a red flag. It’s a stop sign.
Run pip search dowstrike. Yeah, it’s deprecated, but the silence tells you everything.
Then run pip list --outdated and pip-audit. Right now.
That audit will show what’s actually vulnerable (not) what some tool claims to fix.
Most “game-changing” Python tools are just noise layered over broken dependencies.
Your time is finite. Your stack shouldn’t be a guessing game.
The fix isn’t another package.
It’s discipline.
It’s checking before clicking.
It’s asking: What proof do I have this does what it says?
In Python, the most solid module isn’t imported. It’s the one between your ears.
Go audit. Do it today.


 Head of Machine Learning & Systems Architecture
Justin Huntecovil is the kind of writer who genuinely cannot publish something without checking it twice. Maybe three times. They came to digital device trends and strategies through years of hands-on work rather than theory, which means the things they writes about — Digital Device Trends and Strategies, Practical Tech Application Hacks, Innovation Alerts, among other areas — are things they has actually tested, questioned, and revised opinions on more than once.
That shows in the work. Justin's pieces tend to go a level deeper than most. Not in a way that becomes unreadable, but in a way that makes you realize you'd been missing something important. They has a habit of finding the detail that everybody else glosses over and making it the center of the story — which sounds simple, but takes a rare combination of curiosity and patience to pull off consistently. The writing never feels rushed. It feels like someone who sat with the subject long enough to actually understand it.
Outside of specific topics, what Justin cares about most is whether the reader walks away with something useful. Not impressed. Not entertained. Useful. That's a harder bar to clear than it sounds, and they clears it more often than not — which is why readers tend to remember Justin's articles long after they've forgotten the headline.
Head of Machine Learning & Systems Architecture
Justin Huntecovil is the kind of writer who genuinely cannot publish something without checking it twice. Maybe three times. They came to digital device trends and strategies through years of hands-on work rather than theory, which means the things they writes about — Digital Device Trends and Strategies, Practical Tech Application Hacks, Innovation Alerts, among other areas — are things they has actually tested, questioned, and revised opinions on more than once.
That shows in the work. Justin's pieces tend to go a level deeper than most. Not in a way that becomes unreadable, but in a way that makes you realize you'd been missing something important. They has a habit of finding the detail that everybody else glosses over and making it the center of the story — which sounds simple, but takes a rare combination of curiosity and patience to pull off consistently. The writing never feels rushed. It feels like someone who sat with the subject long enough to actually understand it.
Outside of specific topics, what Justin cares about most is whether the reader walks away with something useful. Not impressed. Not entertained. Useful. That's a harder bar to clear than it sounds, and they clears it more often than not — which is why readers tend to remember Justin's articles long after they've forgotten the headline.