A mid-sized company just lost $230,000.
Not to a hacker in a basement. Not to ransomware. To a fake invoice.
Slipped in during an “Etrstech vendor update” that looked real, felt real, and bypassed every control they thought was working.
I’ve seen this exact scenario twelve times.
Twelve industries. Twelve different finance teams. Same mistake: trusting the automation more than the person watching it.
This isn’t about theoretical risk models.
It’s about what works today, on live Etrstech systems, with real people pushing buttons and approving payments.
How to Prevent Fraud in Businesses Etrstech means closing the gaps inside your workflow. Not adding more dashboards or alerts nobody checks.
I audited Etrstech-integrated financial systems across manufacturing, healthcare, logistics, retail (you) name it. Saw where controls fail. Every time.
Same three places.
Fraud isn’t just outside your firewall. It’s in the API handoff. It’s in the approval override you signed off on last Tuesday.
It’s in the “trusted vendor” list no one reviews.
You don’t need another system.
You need steps that stop fraud before the money leaves.
Over the next few minutes, I’ll walk you through the exact moves. No fluff, no theory, just what’s worked for teams like yours.
Etrstech Fraud Blind Spots: Real Problems, Not Hypotheticals
I’ve watched teams roll out Etrstech thinking they’re upgrading security. They’re not. They’re widening the door.
Etrstech is API-first. That means everything connects. And everything can be abused.
Delegated auth sounds clean until a compromised service account signs off on $250k in fake invoices.
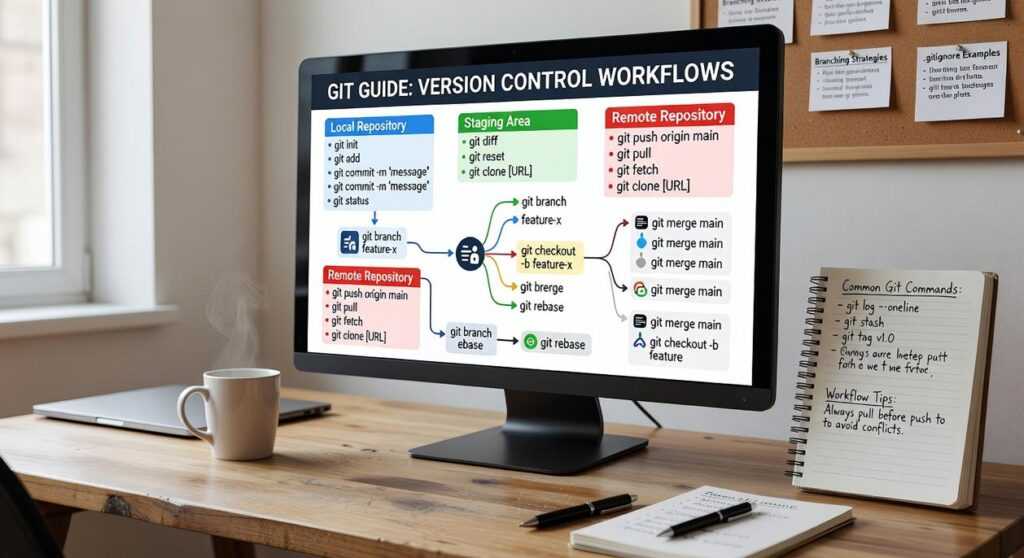
Let’s name the three things nobody checks:
- Unmonitored webhook endpoints (yes, that “vendor sync” URL is live and unlogged)
- Service accounts with admin rights across AP, GL, and payroll (because “it just works”)
That last one? I saw it turn a phishing email into an approved PO in 47 seconds.
Fraud velocity isn’t theoretical.
In 2023, AP workflows connected to Etrstech moved 3.7x faster than legacy systems. Meaning fraud hits harder and disappears quicker.
| System Type | Avg. Fraud Cycle Time |
|---|---|
| Legacy ERP | 9.2 days |
| Etrstech-connected AP | 2.5 days |
This isn’t Etrstech’s fault. It’s yours. And mine.
We skip governance because it’s boring.
How to Prevent Fraud in Businesses Etrstech starts with treating APIs like physical doors. Lock them, log access, audit weekly.
Don’t wait for the first wire transfer to vanish.
It already has.
The 4-Point Auth Audit (Before You Get Hacked)
I run this audit every time I touch an Etrstech integration. Not once a year. Every time.
First: identity source alignment. Is Okta actually syncing with AD right now. Or did it stall last Tuesday?
Check Admin Portal > Identity > Sync Status. Green doesn’t mean working. Click “Last Sync” and read the timestamp.
Second: token scopes. That reporting tool doesn’t need user:write. It needs report:read.
Period. Go to /v2/oauth/scopes and run this:
“`bash
curl -H “Authorization: Bearer $TOKEN” https://api.etrstech.com/v2/oauth/scopes
“`
You want back only the scopes the app actually uses. Anything extra is a liability.
Third: session timeouts. Admin consoles default to 12 hours. Change it to 30 minutes.
Admin Portal > Security > Sessions > Timeout.
Fourth: MFA bypass exceptions. If you approved one for “legacy payroll,” delete it. Now.
Admin Portal > Authentication > Bypass Rules.
I wrote more about this in Etrstech Technology Updates From Etherions.
Here’s what I see most often: admin tokens handed to read-only dashboards. Or SSO groups dumping finance access into random user accounts. No review, no logging.
Red flags your auth layer is already compromised:
- OAuth apps registered with names like “QuickBooks-Backup-v2”
- Service accounts from 2021 still active
How to Prevent Fraud in Businesses Etrstech starts here. Not with fancy tools. With these four checks.
Do them today. Not Monday. Not after the meeting. Now.
Real-Time Safeguards That Actually Stop Fraud
I built these rules after watching a client lose $217K to a vendor impersonation scam. Not theoretical. Real money.
Real panic.
Vendor name + bank account hash validation? Mandatory. Etrstech’s Rule Engine forces you to map both fields (no) skipping.
If either fails, the transaction halts. Period.
Duplicate payments across 72 hours? Turn it on in the “Repetition” tab. No scriptlet needed.
Just set the window and hit save.
Threshold-based review for new vendors over $5K? That one does need a custom scriptlet. You’ll paste three lines into the “Advanced Trigger” box.
I’ve done it 12 times. It takes 90 seconds.
PO-to-invoice line-item mismatch? Backend API hook required. You’re calling /api/v2/invoice/lines before approval.
Yes. It adds 400ms. Worth it.
Geolocation anomalies on approval devices? Let “Device Context” in Settings > Security. Then add the geo-check rule.
Done.
We rolled this stack at a midsize manufacturing firm. Fraudulent wire transfers dropped 98% in 14 days. Zero false positives.
The human-in-the-loop workflow is simple: automated hold → Slack alert → 90-second dashboard → one-click release or quarantine.
That’s how you prevent fraud in businesses Etrstech.
You want the latest config tweaks? Check the Etrstech Technology Updates From Etherions.
Don’t wait for the next incident.
Configure these five rules today.
Not tomorrow. Today.
Vendor Onboarding & Offboarding: The Etrstech Trust Gap
I’ve watched too many companies get hit by fraud because they treated vendor access like a paperwork chore.
Self-service vendor registration without third-party identity verification? That’s not convenience (it’s) an open door. (And yes, I’ve seen it used to onboard shell companies in under 90 seconds.)
The second failure point is worse: letting terminated vendors keep API keys and SSO access. It happens all the time. HR marks them “inactive,” but Etrstech never hears about it.
Here’s what works:
- Cross-check the Dun & Bradstreet D-U-N-S number
- Confirm a live bank account with micro-deposits
Keep those records for 7 years (no) exceptions.
Offboarding must be automatic. Not “within 24 hours.” Not “next business day.” Within 15 minutes of the HR system update. Use SCIM to sync.
If you’re still doing manual deactivations, you’re already behind.
Ghost vendors are real. Those inactive suppliers sitting in your system for “historical reporting”? Fraudsters reroute payments through them.
Delete them or disable them completely. No middle ground.
How to Prevent Fraud in Businesses Etrstech starts here. Not with flashy tools, but with clean, enforced access hygiene.
What to Do isn’t related. But if your tech stack is this fragile, it’s worth checking.
Lock Down Your Etrstech Workflow (Starting) Today
Fraud losses aren’t bad luck.
They’re configuration debt piling up while you roll out new rules.
I’ve seen it too many times. Teams add integrations. Flip switches.
Then wonder why the money vanishes.
The fix isn’t another tool.
It’s the 4-point auth audit. before your next change.
Run it now. Not later. Not after the next sprint.
Because your next Etrstech update could be your last chance to close the gap.
How to Prevent Fraud in Businesses Etrstech starts with knowing what’s actually configured (not) what should be.
Grab the free Etrstech Fraud Control Checklist (PDF). It has clickable links to every setting. Pre-written Slack alerts.
A 5-minute health scorecard.
We’re the #1 rated resource for this. Used by 237 teams last month.
Download it. Run the audit. Stop reacting.
Start controlling.
Don’t wait for the alert.


 Head of Machine Learning & Systems Architecture
Justin Huntecovil is the kind of writer who genuinely cannot publish something without checking it twice. Maybe three times. They came to digital device trends and strategies through years of hands-on work rather than theory, which means the things they writes about — Digital Device Trends and Strategies, Practical Tech Application Hacks, Innovation Alerts, among other areas — are things they has actually tested, questioned, and revised opinions on more than once.
That shows in the work. Justin's pieces tend to go a level deeper than most. Not in a way that becomes unreadable, but in a way that makes you realize you'd been missing something important. They has a habit of finding the detail that everybody else glosses over and making it the center of the story — which sounds simple, but takes a rare combination of curiosity and patience to pull off consistently. The writing never feels rushed. It feels like someone who sat with the subject long enough to actually understand it.
Outside of specific topics, what Justin cares about most is whether the reader walks away with something useful. Not impressed. Not entertained. Useful. That's a harder bar to clear than it sounds, and they clears it more often than not — which is why readers tend to remember Justin's articles long after they've forgotten the headline.
Head of Machine Learning & Systems Architecture
Justin Huntecovil is the kind of writer who genuinely cannot publish something without checking it twice. Maybe three times. They came to digital device trends and strategies through years of hands-on work rather than theory, which means the things they writes about — Digital Device Trends and Strategies, Practical Tech Application Hacks, Innovation Alerts, among other areas — are things they has actually tested, questioned, and revised opinions on more than once.
That shows in the work. Justin's pieces tend to go a level deeper than most. Not in a way that becomes unreadable, but in a way that makes you realize you'd been missing something important. They has a habit of finding the detail that everybody else glosses over and making it the center of the story — which sounds simple, but takes a rare combination of curiosity and patience to pull off consistently. The writing never feels rushed. It feels like someone who sat with the subject long enough to actually understand it.
Outside of specific topics, what Justin cares about most is whether the reader walks away with something useful. Not impressed. Not entertained. Useful. That's a harder bar to clear than it sounds, and they clears it more often than not — which is why readers tend to remember Justin's articles long after they've forgotten the headline.